 Crytoanalysts have struggled for 12 years on "encrypted notes" found on murder victim.
Crytoanalysts have struggled for 12 years on "encrypted notes" found on murder victim.
McCormick's family said that this was common for him, as he used to write coded notes since he was a boy and never revealed the secret to decipher them. The FBI believes the contents of the notes might have information about his whereabouts and activities in the days leading up to his murder, and are appealing to the public for help.
It is looking for "left-field" ideas on how McCormick may have encrypted the note that they never thought of, or samples of other notes written using unconventional methods. "We are really good at what we do," said Cryptanalysis and Racketeering Records Unit (CRRU) chief Dan Olson, "but we could use some help with this one."
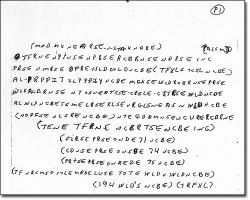
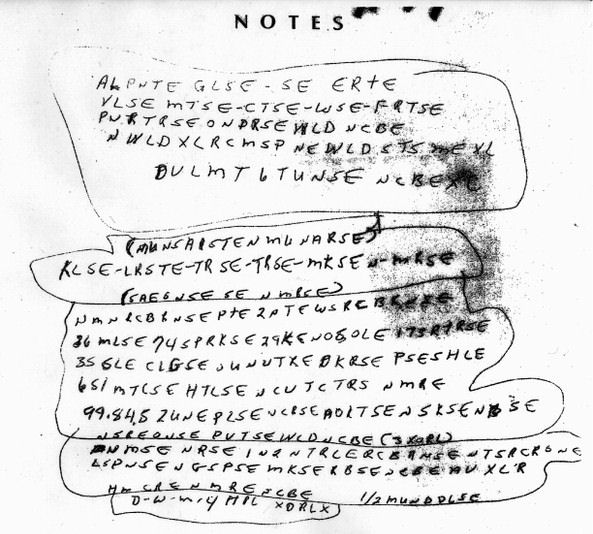
Note 1
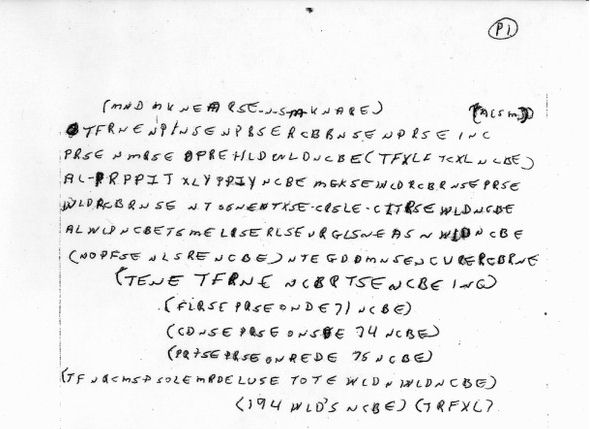
Note 2
For more Information: FBI.gov













