 Over the past couple of days, law enforcement has taken further action against the Cryptolocker ransomware.
Over the past couple of days, law enforcement has taken further action against the Cryptolocker ransomware.
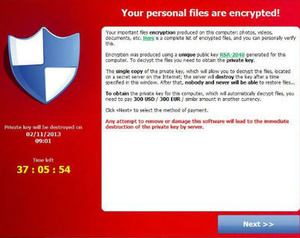
Cryptolocker is a nasty piece of work that encrypts personal files on a victim's PC and will not decrypt them until a ransom is paid, typically 1 bitcoin which could cost you around $600. The malware will even destroy files if the user does not pay up on time. It is estimated to have cost consumers and businesses over $30 million since last summer.
The ransomware was often delivered to a victim's PC through the Gameover ZeuS botnet, but it also spread through malicious e-mails.
The effect of the GOZeuS and Cryptolocker take-down
According to Danish security firm Heimdal Security, which was named by the FBI as an important collaborator against Cryptolocker, the number of estimated new infections per day of Cryptolocker has fallen from around 8,000 to close to zero. Of course, it cannot be absolutely sure of the figures but the infection rate has certainly plummeted.
Law enforcement has warned Internet users that they have a roughly two week window to clean-up GOZeuS and Cryptolocker infections before cybercriminals may be able to wrestle back some control. You can find instructions to detect and remove GOZeuS right here.
In future, a debate may arise about the role of Internet Service Providers in disrupting botnets, with one researcher already saying ISPs need to start quarantining infected computers now until they are cleaned up.
It is not just Windows PCs that are vulnerable to attacks like this either. Just today, ESET published an analysis of the first ransomware for Android phones and tablets that encrypts users' personal files and won't decrypt them unless a ransom fee is paid.
The U.S. has identified, charged and is pursuing a 30-year old Russian man it alleges to have been the top administrator of GOZeuS and Cryptolocker.













